Drupal Warns of Multiple Critical Vulnerabilities
Drupal issued a security advisory of four critical vulnerabilities rated from moderately critical to critical. The vulnerabilities affect Drupal versions 9.3 and 9.4.
The security advisory warned that the various vulnerabilities could allow an hacker to execute arbitrary code, putting a site and server at risk.
These vulnerabilities do not affect Drupal version 7.
Additionally, any versions of Drupal prior to 9.3.x have reached End of Life status, which means that they are no longer receiving security updates, making them risky to use.
Critical Vulnerability: Arbitrary PHP Code Execution
An arbitrary PHP code execution vulnerability is one in which an attacker is able to execute arbitrary commands on a server.
The vulnerability unintentionally arose due to two security features that are supposed to block uploads of dangerous files but failed because they didn’t function well together, resulting in the current critical vulnerability which can result in a remote code execution.
Access Bypass Vulnerability
This vulnerability, rated as moderately Critical, allows an attacker to alter data that they’re not supposed to have access to.
According to the security advisory:
“Under certain circumstances, the Drupal core form API evaluates form element access incorrectly.
…No forms provided by Drupal core are known to be vulnerable. However, forms added through contributed or custom modules or themes may be affected.”
Multiple Vulnerabilities
These are some of the potential issues:
- Arbitrary PHP code execution
- Cross-site scripting
- Leaked cookies
- Access Bypass vulnerability
- Unauthorized data access
- Information disclosure vulnerability
Updating Drupal Recommended
The security advisory from Drupal recommended immediately updating versions 9.3 and 9.4.
Users of Drupal version 9.3 should upgrade to version 9.3.19.
Users of Drupal version 9.4 should upgrade to version 9.4.3.
Source: Drupal Warns of Multiple Critical Vulnerabilities
How to set up Performance Max campaigns the right way
What is Performance Max?
PMax is an all-in-one campaign type that displays ads across all of Google’s channels:
- YouTube.
- Display.
- Search.
- Shopping.
- Discover feed.
- Gmail.
- Maps.
Note: Smart Shopping and Local campaigns will be depreciated and rolled into PMax shortly.
What is different about PMax?
There are differences in campaign structure. Most notably in terms of Structure:
- Ad Groups → Asset Groups
- Product Groups → Listing Groups
Why use Performance Max campaigns?
For ecommerce retailers who’ve seen success with Smart Shopping, PMax takes it to the next level by adding additional placements and reach – acting as a Smart Shopping campaign with retargeting and prospecting display ads layered on top of it.
For lead generation, Performance Max can deliver scale and efficiency that may be hard to achieve through Search and Display alone.
Upgrading from Smart Shopping Campaigns
If you’ve been using Smart Shopping Campaigns, it’s recommended to use the one-click upgrade tool in the Recommendations tab. Using this tool will sync the campaign’s historical performance in the back-end which enables PMax to hit the ground running.
Campaign Structure
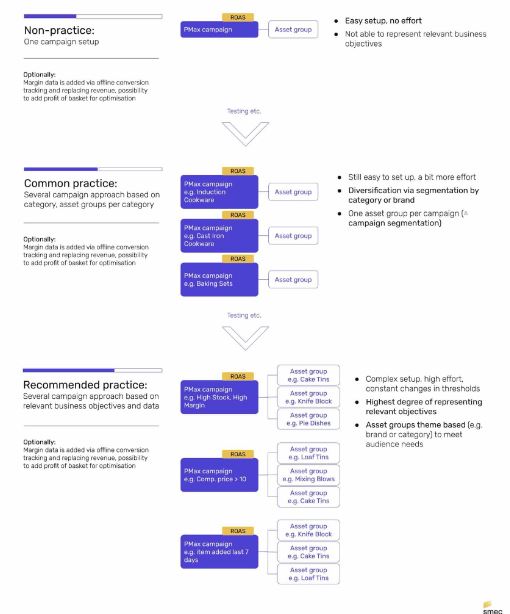
Below is a great chart from Mike Ryan illustrating campaign structure ideas:
Conversion Goals
Choose the conversion actions that make sense for your business.
- Ecommerce/Shopping: Choose “Purchases”
- Lead-Gen/Services: Choose calls, forms, chats etc
Hot tip: To improve lead quality, focus on calls over forms/chats.
Location Targeting
When setting up your campaign, after choosing your targeted locations, make sure to select Presence: People in or regularly in your targeted locations
Asset Groups
Your messaging and creative assets should be tightly themed to the product or service within the group.
If you don’t provide a video, Google will make a horrible one for you. Highly recommend creating something basic using Canva or a similar tool.
For ecommerce, something worth testing for Google Shopping, especially if you’ve seen success with Smart Shopping historically, is to launch a PMax campaign with no assets aside from the data feed.
Note: You’ll likely need to create a new Asset Group.
Exclusions
- Customer Exclusions: Upload your customer list and have the system exclude them from all targeting. This is useful if you want to focus on new customer acquisition.
- Keywords: If you have a Google rep, they can block branded search terms from PMax for you.
Audience Signals
Audience signals are different from Audience targeting. The system uses this as a signal to find your ideal prospective customer.
Data feed
For ecommerce, the most important piece of the puzzle is the product information. While everything else helps, the data feed submitted to Google Merchant Center can have the largest impact on your Performance Max campaign performance
Bid strategies
Performance Max has the following two options available:
- Maximize Conversions (with optional target CPA)
- Maximize Conversion Value (with optional target ROAS)
If your account already has lots of historical data, you can jump right into target CPA/ROAS. With a new account, start with Maximize Conversions so the system can gather data. Later on, once you’re seeing steady conversions, switch to tCPA or tROAS to hit your goals.
Source: How to set up Performance Max campaigns the right way
SiteCare Acquires Maintainn from WebDevStudios
More consolidation is happening in the WordPress maintenance services space, as SiteCare announced it has acquired Maintainn, a long-time competitor, from WebDevStudios.
As WebDevStudios began focusing more on taking on larger, more technical projects that run WordPress at scale for clients like The Wall Street Journal, Starbucks, Microsoft, Viacom, and the NBA, the company struggled to effectively market Maintainn with messaging that conveyed its distinction from WebDevStudios’ enterprise development offerings.
Maintainn’s current maintenance plan customers, which range from $49-$249/month, will remain at the same pricing for one year. SiteCare may reevaluate these pricing tiers in the future. Customers are promised the same level of service as their current plan but may also receive some enhanced benefits that they had not received before. In addition to maintenance services, SiteCare also offers its customers a range of digital marketing services.
This is SiteCare’s second acquisition of a WordPress site management company after acquiring WP Site Care in 2018. The company will take on all of Maintainn’s assets but the employees will remain with WebDevStudios.
Source: SiteCare Acquires Maintainn from WebDevStudios
Thousands of Twitter accounts put up for sale on the dark web

Account details of more than five million Twitter users are being sold on the dark web forums for $30,000.
The threat actor, going by the astonishingly creative alias “devil” is selling data on 5.4 million users, apparently obtained by exploiting a vulnerability discovered in January 2022.
Twitter has apparently patched the hole, and even compensated the person that found it, going by the name “zhirinovskiy”, $5,040.
Investigating the leak
The database includes public-facing data, email addresses used to register the account, and phone numbers. While not having passwords included in the data set definitely helps with security, email addresses and phone numbers could still be used for other forms of phishing, identity theft, and maybe even full account takeover.
The seller claims the database includes sensitive information on “Celebrities, Companies, randoms, OGs, etc.” It was also said that a sneek peak of the database was posted on the data breach discussion and leaks forum, Breach Forums, where its authenticity was confirmed.
Twitter said it was investigating the issue, but has refrained from any further comment so far.
The microblogging social network has been making headlines lately, as it goes back and forth with eccentric billionaire Elon Musk over his potential acquisition of the platform.
While initially, the Tesla CEO expressed his intent to buy the little blue bird, he decided to pull out, as it appears Twitter did not share exact data on the number of bots and fake accounts on the network, or how it plans to cut down on this type of fraud.
Twitter’s management still stands by its earlier reports that bots make up less than five percent of all accounts on Twitter. According to Business Of Apps, Twitter has some 450 million active users.
Source: Thousands of Twitter accounts put up for sale on the dark web
More News:
Research: Latest digital marketing trends to better connect with customers
Facebook Home tab to show more content recommendations
Google adds automated messaging through Business Profiles frequently asked questions



